Over the past months, coordinated DDoS campaigns linked to groups such as NoName057(16) have expanded across Europe. Through what is known as the DDoSia project, volunteers are recruited and orchestrated to launch distributed denial of service attacks against public institutions and private organizations.
Recent guidance from CISA highlights how these campaigns are affecting government entities and critical sectors. The visible impact is availability disruption. Websites become unreachable. Public portals go offline.
For industrial operators, however, this is not primarily a traffic problem.
It is an exposure problem.
And exposure in Operational Technology has structural consequences.
Understanding the Mechanics Behind DDoSia
DDoSia is not a traditional malware driven botnet. It is a coordinated volunteer model. Participants run a client that receives target instructions from orchestration infrastructure and generates traffic accordingly.
From a technical perspective, the campaign relies on three pillars:
- Discovery
- Coordination
- Amplification
Before traffic is generated, targets are identified and validated. Infrastructure is scanned. Services are enumerated. Responsive systems are catalogued.
This reconnaissance phase is not unique to DDoSia. It is common across hacktivist ecosystems. What is different today is scale and speed. Enumeration happens continuously, often through automated tooling and distributed volunteer nodes.
In that process, exposed OT and SCADA systems are frequently identified.
Not because they are the primary objective, but because they are reachable.
And reachability is the first prerequisite for weaponization.
Why OT Environments Are Structurally Exposed
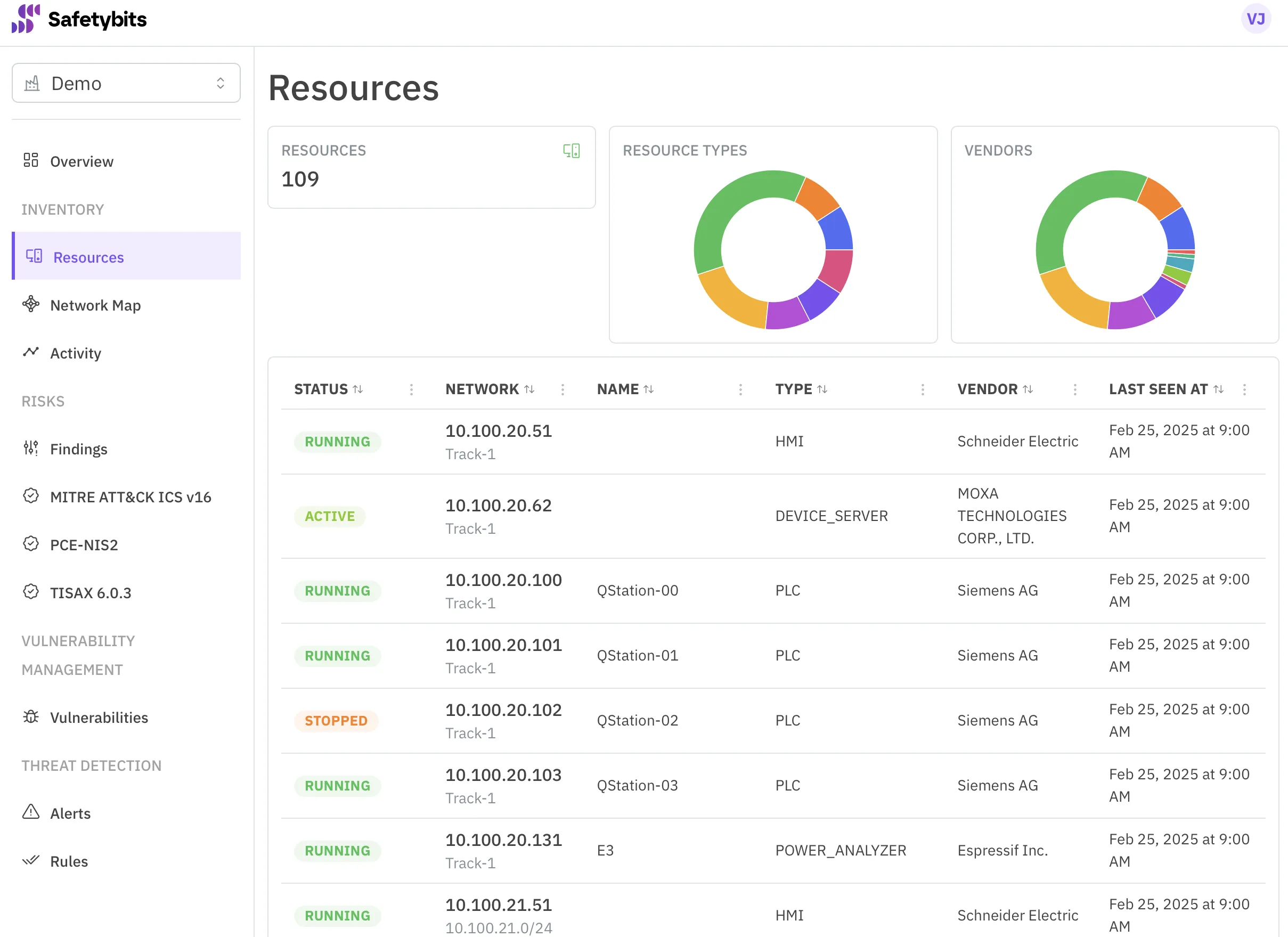
Industrial environments have evolved significantly over the last decade.
- Remote vendor maintenance
- External engineering access
- Cloud based analytics
- Centralized monitoring platforms
- IoT integration across facilities
Each connection solves an operational challenge. Collectively, they expand the attack surface.
From a security research perspective, the issue is rarely a single misconfiguration. It is exposure drift over time.
- Temporary firewall exceptions remain permanent
- Remote access ports stay open after projects conclude
- Legacy web interfaces continue responding externally
- Authentication models are not upgraded when connectivity changes
Most organizations inventory assets internally. Few continuously validate what is externally reachable from the internet.
That gap is what campaigns like DDoSia expose.
Can a DDoS Campaign Stop a Plant
In traditional industrial control system architectures, core control loops operate locally. PLC logic continues executing even if WAN connectivity fails. Safety instrumented systems remain independent.
However, availability disruption can still create operational consequences.
- If centralized monitoring becomes unreachable, operators may lose real time visibility
- If remote engineering access fails, maintenance response slows
- If external connectivity is required for coordination across sites, disruption propagates
More importantly, exposure discovered during a campaign can trigger emergency containment measures. Organizations may isolate segments abruptly once they realize industrial services are publicly accessible.
Operational impact often results from reactive containment, not from the DDoS traffic itself.
That distinction matters.
Infrastructure Abuse Is the Real Risk
From an analytical standpoint, the more relevant question is not whether DDoS traffic reaches your perimeter.
It is whether your industrial infrastructure is externally visible and therefore available to be leveraged.
- If a SCADA gateway responds on the public internet, it can be indexed
- If an HMI exposes a login panel without strong authentication, it can be captured
- If an IoT device bridges operational and external networks, it can be repurposed
Weaponization does not require advanced ICS malware. It requires visibility combined with unmanaged security posture.
This pattern is not new. In cloud environments, exposed workloads were routinely repurposed for cryptomining. The objective was not data theft but resource exploitation. The same principle applies in industrial contexts. When operational assets are visible and insufficiently governed, they can be leveraged for purposes entirely unrelated to their intended function. DDoS amplification is simply the latest expression of a broader infrastructure abuse model.
In several hacktivist campaigns, public proof of access has been used as psychological leverage. Screenshots, device banners, camera feeds. Even limited access can create reputational damage disproportionate to the technical intrusion.
This is why exposure governance is strategic, not tactical.
Why Traditional Monitoring Misses This
Security operations typically rely on internal telemetry. Logs, events, alerts generated within the perimeter.
Network operations monitor throughput and availability.
Compliance teams perform periodic reviews.
What is often missing is continuous external validation of posture.
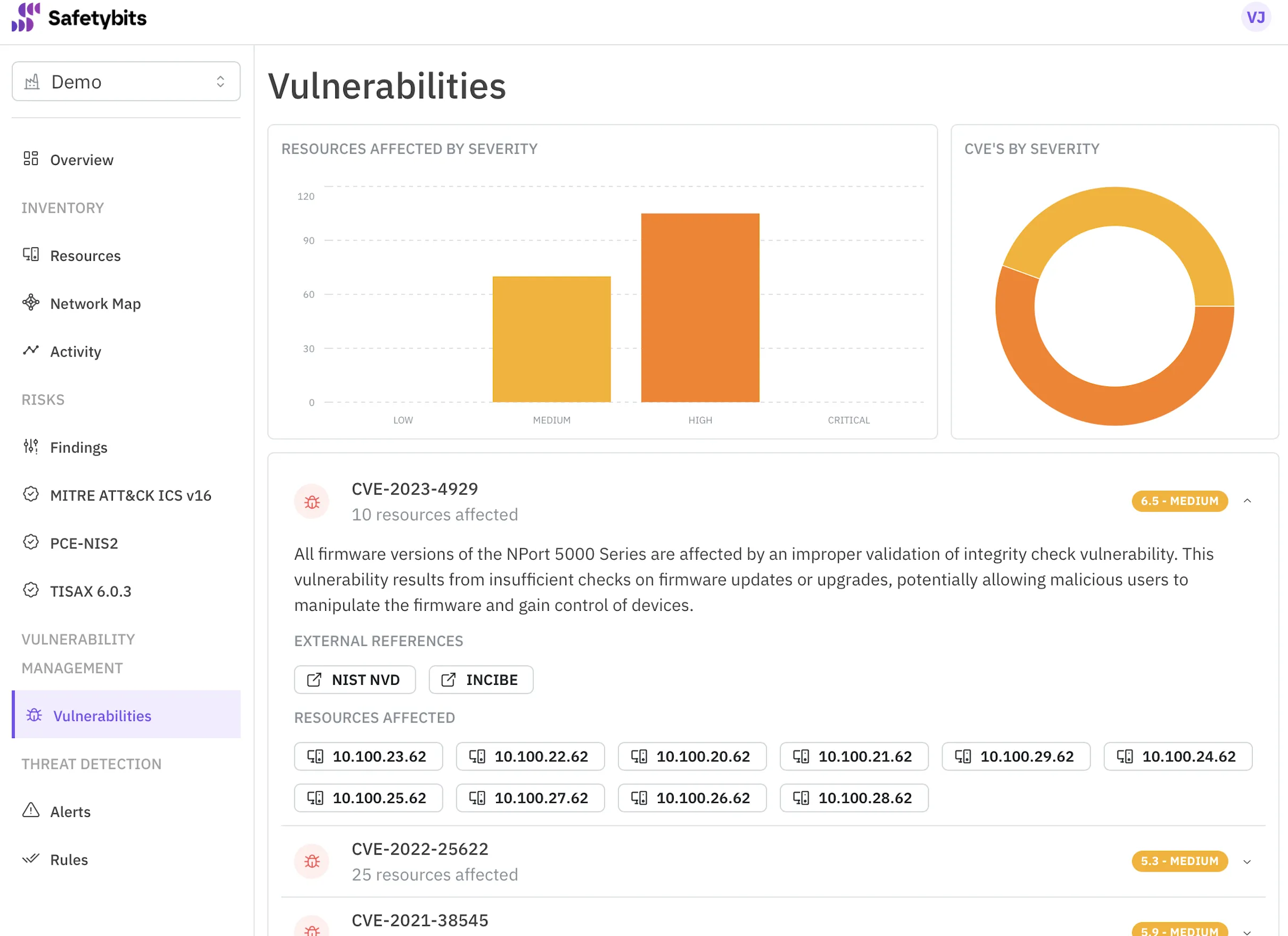
- Which industrial services are internet reachable today
- Which new exposure appeared after the last maintenance window
- Which vulnerabilities are tied to exposed assets
- Which outbound communications originate unexpectedly from OT segments
Without this external perspective, organizations operate with partial visibility.
Campaigns like DDoSia do not create exposure. They reveal it.
The Role of OT Security Posture Management
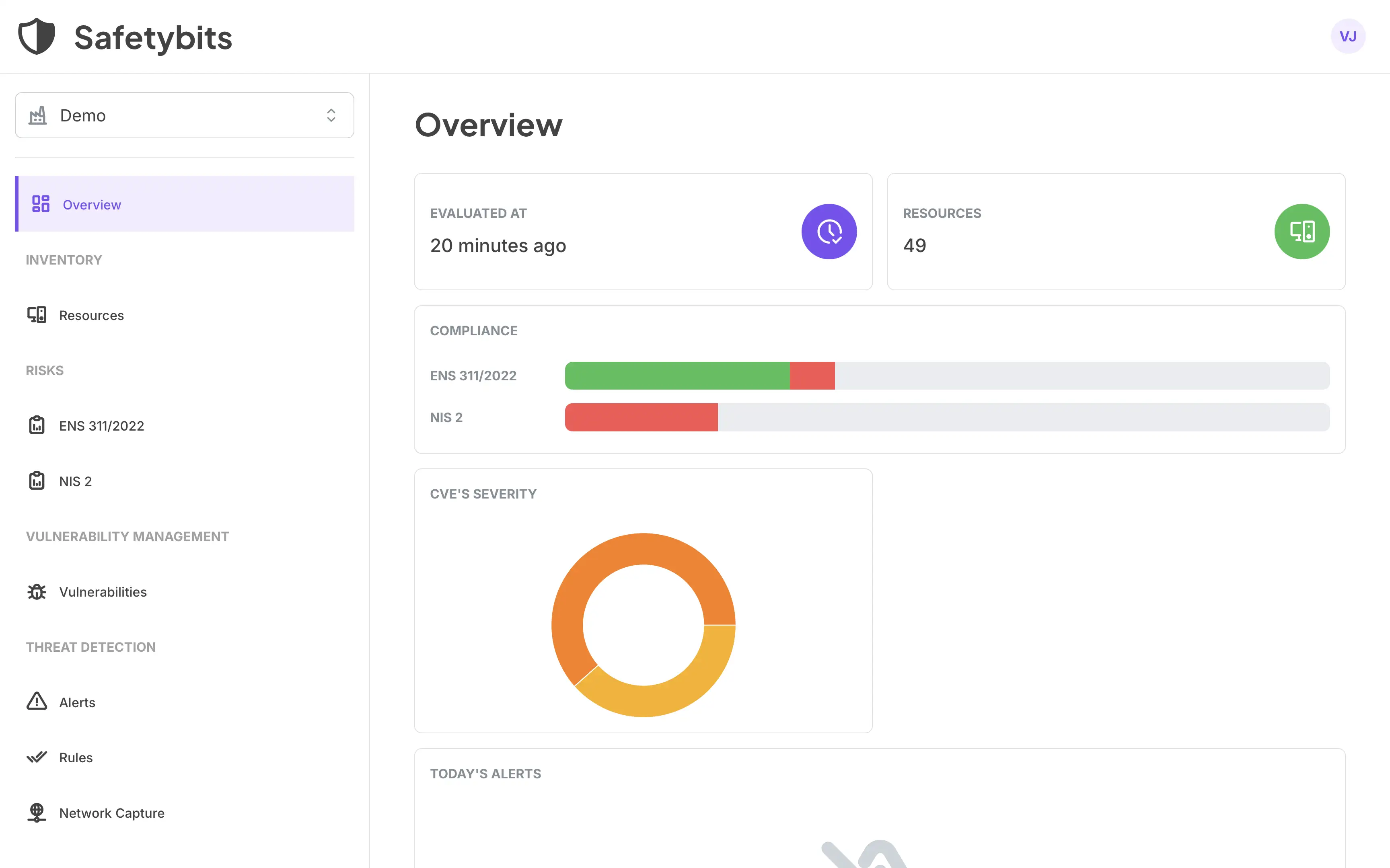
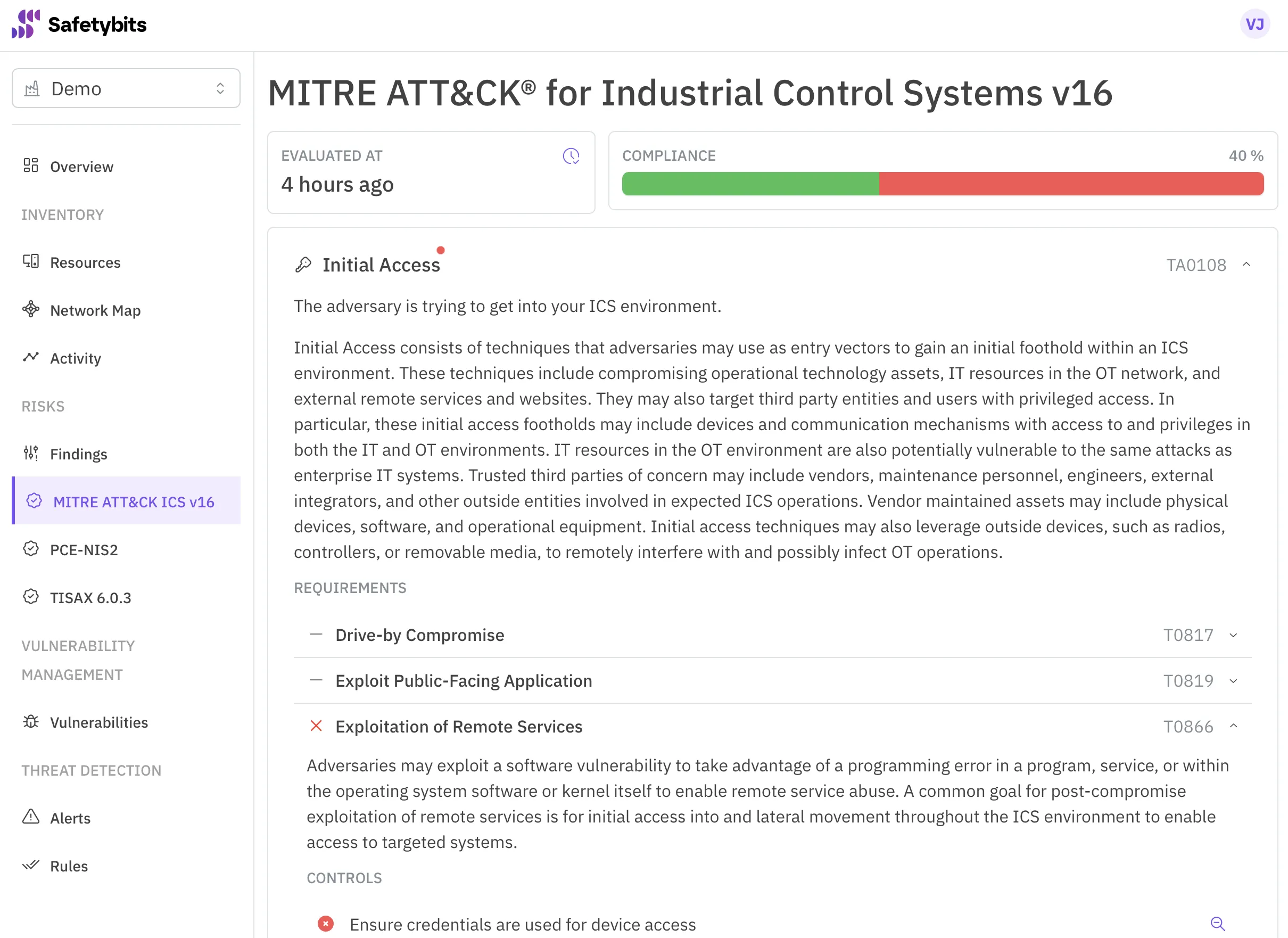
An Operational Technology Security Posture Management approach addresses this structural weakness.
It focuses on:
- Continuous asset discovery across operational domains
- Detection of configuration drift before it becomes public exposure
- Correlation of vulnerability state with real world reachability
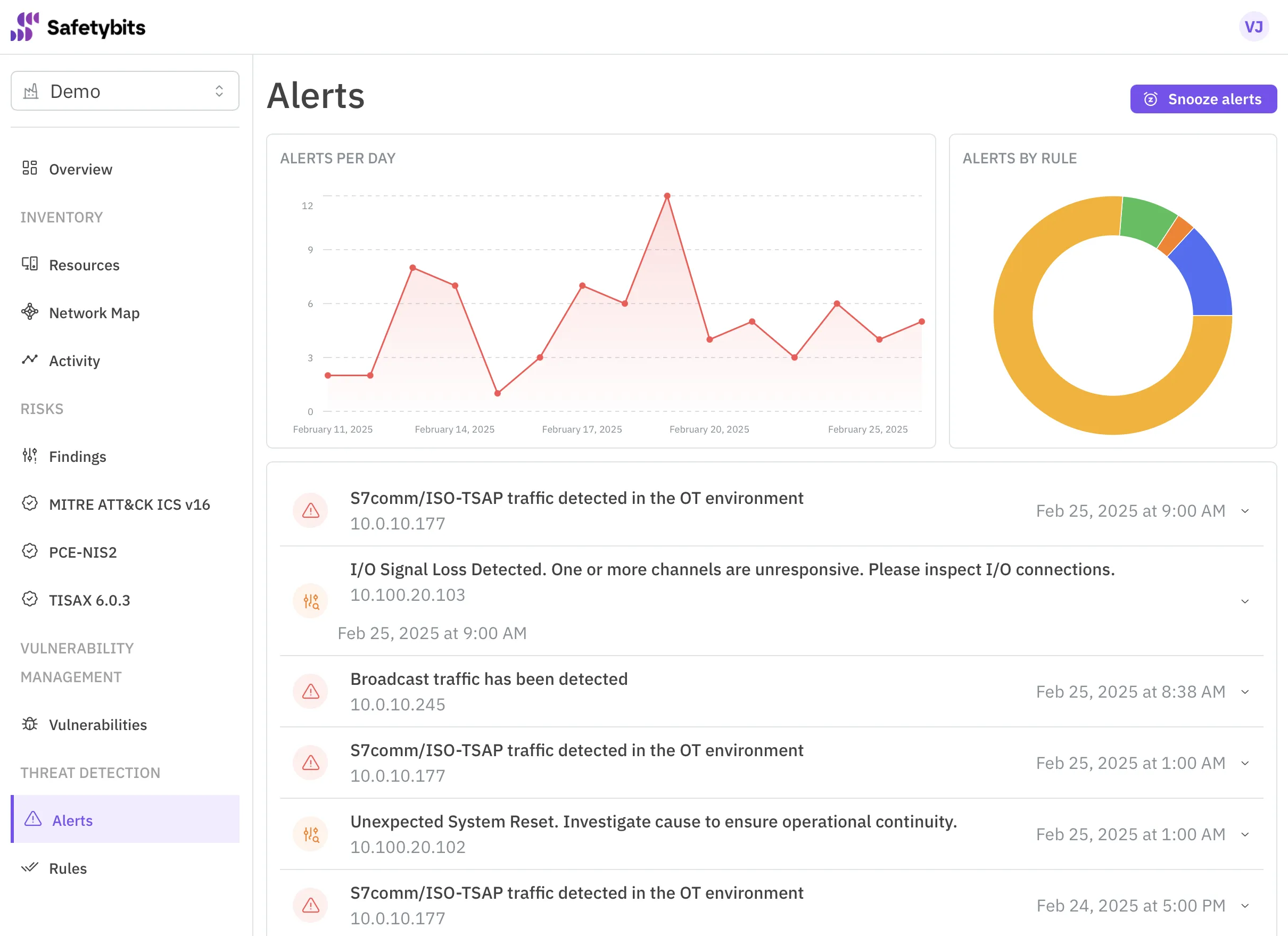
- Precision alerts when posture changes
- Mapping findings to regulatory and risk obligations
In addition, posture management must extend beyond static configuration. Detecting newly established outbound connections from operational segments, identifying unexpected HTTP communications, and applying machine learning driven rules combined with deep packet inspection provides early indication that an industrial asset may be communicating outside its intended operational profile.
This is not about reacting once traffic spikes. It is about ensuring that industrial infrastructure cannot be unintentionally weaponized.
At Safetybits, this is the lens we apply. We help industrial organizations understand their security posture continuously, not periodically. We combine asset visibility, vulnerability context, risk governance, and behavioral threat detection into a unified operational model.
Because resilience in OT is not only about preventing intrusion.
It is about governing exposure before someone else finds it.
A Necessary Shift in Perspective
DDoSia is a signal. It demonstrates how quickly coordinated actors can scale disruption and how exposed infrastructure becomes leverage in geopolitical conflict.
For industrial organizations, the strategic question is simple.
Is your OT environment continuously governed, or only periodically reviewed?
Availability matters. But unmanaged exposure is what turns infrastructure into a weapon.
Industrial resilience begins with visibility.
And visibility must be continuous, correlated, and operationalized.
Expand your reach with OTSPM
The narrower your view, the less risks you can detect. Discover how an OTSPM platform leverages correlation to expand your reach.
Discover more →